 [ad_1]
[ad_1]
Hackers are now using software developed by the US National Security Agency (NSA) to illegally extract cryptocurrencies. According to a recent report published by the Cyber Threat Alliance (CTA), compiled by a collective of computer security experts from McAfee, Cisco Talos, NTT Security, Rapid7 and Sophos, among others, cryptographic malware detections have passed 400% in the last one and a half years.
The malicious actors are overwhelming the resources of the computer processor through intrusions of internet network infrastructure and computer hacks, among other means. One of the most worrying trends is the use of an NSA exploit leaked at the beginning of last year by Shadow Brokers dubbed EternalBlue.
Immediately after the release of its source code, cybercriminals used the tool to launch a devastating ransomware attack dubbed WannaCry, which resulted in more than 200,000 infected computers in over 100 countries. The British National Health Service (NHS) was one of the institutions affected by the attack and suffered a network shutdown.
According to new reports, the same exploit is used to exploit the power of mining encryption using malware called WannaMine. Computers that have been infected can slow down or experience problems with hardware overheating. However, some attacks are more sophisticated. They monitor the use of the mouse or the CPU and automatically interrupt operations when power processing exceeds a certain threshold.
This feature makes them harder to detect, allowing them to persist and ultimately generate more returns for cybercriminals. Generally, EternalBlue malware infections are difficult to detect due to their ability to function without downloading secondary application files.
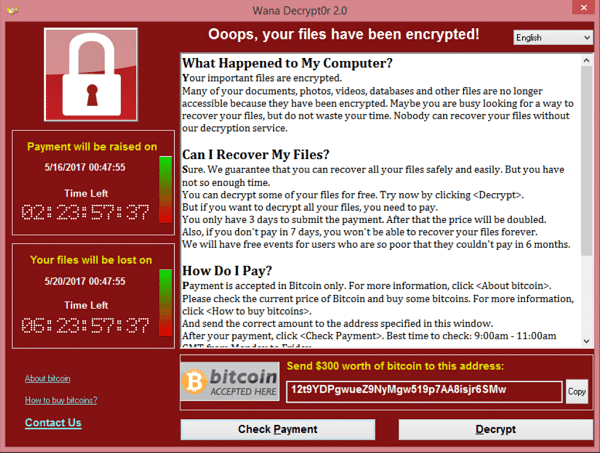
The WannaCry malware has caused the infection of over 200,000 computers in over 100 countries. (Image credit: Wikipedia).
How WannaMine Crypto Mining malware works
WannaMine is the most famous crypt-mining malware based on EternalBlue. It turned out that it spreads through various means. One of these is from Internet users who download counterfeit software from unofficial sources, email attachments and offer misleading software update suggestions.
It relies on Windows management tools for its operations and camouflages itself within legitimate processes. As such, it does not work on Android or iOS devices. However, it allows an attacker to download and upload files to a computer, enumerate running processes, execute arbitrary commands, collect system-specific information such as IP addresses and computer name, and allow the intruder to change some settings of the device.
Wannamine typically uses Mimikatz, a Windows hacking tool used to "crack" the software, to get more control of the system. Originally developed by Benjamin Delpy, Mimikatz can access the passwords of a computer through his memory and make it a slave to a botnet. It also has the ability to export security certificates, perform Microsoft AppLocker overrides and software restriction processes in the software, as well as modify privileges.
Cryptojacking statistics
The practice of cryptojacking is apparently rampant and last November the statistics published by AdGuard stated that more than 33,000 websites with a total of over 1 billion monthly visitors had cryptographic scripts. Most have not bothered to warn users of this. It is said that Monero is the cryptocurrency preferred by cryptojacking actors mainly because of its pseudonymisation features and the ability to be extracted using medium-low end computers.
In February, over 34,000 websites were found using CoinHive's JavaScript miner, which was also used to extract Monero. This was according to statistics derived from the PublicWWW search database, which can be used to reveal JavaScript snippets on websites.
The CoinHive miner is a widely legitimate way to undertake mining in the browser. Currently, only about 19,000 Web pages are listed as characterized by the Coinhive code. The sharp decline in websites that use the miner is probably correlated with the decline in mining profitability.
Away from Coinhive, the miner Smominru Monero turned out to be the most active in nature and is disseminated using EternalBlue exploits. Its use was first reported in May of last year and, at that time, the actors behind it would have ousted $ 8,500 of Monero in a week. Their botnet network consisted of over 526,000 infected nodes, which looked like servers located in Taiwan, Russia, and India.
Protection against mining encryption attacks
Protecting a PC from EternalBlue-based malware-based malware attacks is simple, by regularly updating Windows and scanning for viruses using Windows Defender Antivirus. PC users should also avoid the use of "cracked" software because many create backdoor access for hackers.
reported
[ad_2]Source link